Introduction
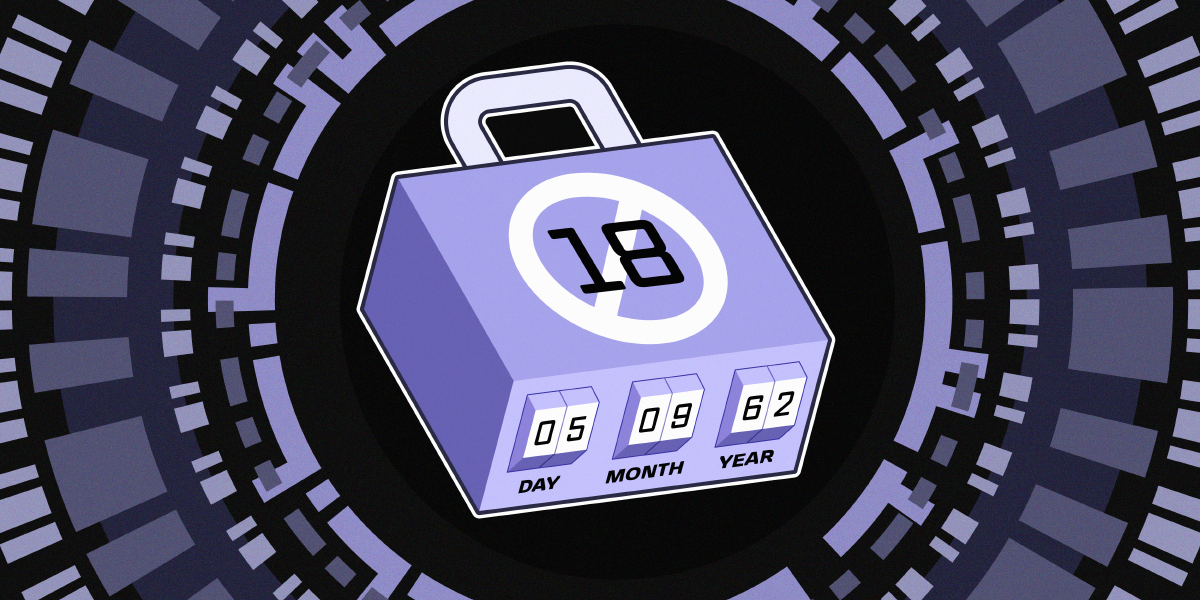
In early 2025, the Electronic Frontier Foundation (EFF) joined 18 organizations—including Mozilla, the Tor Project, and Open Rights Group—in sending a letter to UK policymakers. The message: tackling online harm effectively means addressing its root causes, not imposing sweeping restrictions like universal age-gating that risk reshaping the open web for the worse. This step-by-step guide distills that coalition’s insights into a practical roadmap for policymakers, advocates, and concerned citizens who want to craft rights-respecting online safety policies. Follow these steps to prioritize real solutions without sacrificing the internet’s openness or user privacy.
What You Need
- A basic understanding of digital rights principles (privacy, anonymity, free expression)
- Access to policy briefs from organizations like EFF, Mozilla, or Open Rights Group
- Engagement with at least one technical expert on age assurance systems and their limitations
- Willingness to challenge business models that prioritize engagement over safety
- A commitment to preserving the internet’s core qualities: interoperability, accessibility, and openness
Step-by-Step Guide
Step 1: Recognize the Flaws in Blanket Age-Gating Approaches
The Children’s Wellbeing and Schools Bill in the UK has sparked proposals for sweeping age-gating requirements. Before adopting such measures, study the evidence: current age assurance technologies are either inaccurate, privacy-invasive, or both. Mandating them across social media, video games, VPNs, and even basic websites forces all users to verify their identity just to access the web. This opens the door to expanded surveillance, data breaches, and the erosion of anonymity. Ask yourself: Is forcing a 70-year-old to prove her age to read a blog really necessary to protect children?
Step 2: Identify the Root Causes of Online Harm
Many digital platforms are designed to maximize engagement and profit through pervasive data collection and targeted advertising. These systemic practices often come at the expense of user safety and autonomy. Instead of focusing on access bans, analyze the business models that drive harmful content. For example, algorithms that recommend extreme content to increase watch time are a root cause—yet they are rarely addressed in age-gating proposals. As the coalition letter notes, meaningful efforts must tackle these underlying drivers rather than imposing surface-level restrictions.
Step 3: Design Rights-Respecting Accountability Measures
Hold companies accountable for their design choices, not just for user age. Propose policies that require platforms to conduct privacy impact assessments, limit data collection by default, and use algorithms that prioritize safety over engagement. Consider transparency mandates: platforms should publish reports on how their systems amplify harmful content. The goal is to shift the burden from individual users (who would have to verify their identity) to companies (who should design safer systems from the start). This aligns with the coalition’s call for “user rights by design.”
Step 4: Preserve the Internet’s Open Architecture
Age-gating at scale would fragment the web into a patchwork of restricted jurisdictions, limit access to information, and entrench powerful gatekeepers like app stores and platform ecosystems. Evaluate the unintended consequences: will a 13-year-old seeking LGBTQ+ support resources be blocked by a regional age wall? Will activists in repressive countries be forced to show ID to use a VPN? Policymakers must ensure that any new rule does not weaken interoperability, accessibility, and openness—the very qualities that make the internet a global public resource. As the signatories warned, these changes could fundamentally reshape the internet in harmful ways.

Step 5: Engage with Stakeholders and the Public
Effective policy requires input from those directly affected. Host roundtables with civil society groups, technologists, young people, and privacy advocates. The coalition’s letter highlights that the internet remains a vital space for youth—offering information, support networks, and expression opportunities not available offline. Policies that restrict access risk cutting off these lifelines without meaningfully reducing harm. Use public consultations to gather diverse perspectives, and communicate clearly that protecting users online requires more than heavy-handed restrictions.
Tips for Success
- Start small, test often: Pilot any age-assurance initiative in a limited setting before scaling. Measure both safety outcomes and privacy impacts.
- Don’t confuse correlation with causation: Age restrictions might reduce some harms, but the data often shows they displace rather than solve the problem. Focus on root causes like algorithmic amplification.
- Collaborate internationally: Online harm is a global issue. Coordinate with other jurisdictions (EU’s Digital Services Act, for instance) to avoid fragmented regulations that weaken the open web.
- Prioritize transparency: If age assurance is unavoidable, require that systems be open-source, auditable, and limited in data retention. Users deserve to know how their information is being used.
- Remember the goal: The aim is to reduce harm, not to create a surveillance infrastructure. Every policy should be measured against whether it genuinely protects vulnerable users without sacrificing fundamental rights.
For more context, refer back to Step 1 for a deeper look at age-gating risks, or revisit Step 5 for stakeholder engagement strategies.