Managing X.509 certificates across an enterprise often feels like juggling two separate worlds: internal private keys for microservices and public trust for customer-facing sites. IBM Vault bridges this divide with its new public CA orchestration, enabling a single, automated workflow for every certificate. Below, we answer key questions about this capability and its impact on security, compliance, and operational efficiency.
What challenge does fragmented certificate management create for enterprises?
Fragmented certificate management forces teams to use separate tools and manual processes for private versus public certificates. With HashiCorp Vault (now IBM Vault) automating private PKI internally, public certificates still require manual requests, renewals, and revocations through external CA portals. This creates a dual-track system that increases operational overhead, introduces human error, and leads to missed renewals. The lack of a unified view means expiration dates are scattered across providers, turning each certificate into a potential outage clock. Governance becomes siloed, making it impossible to enforce consistent security policies or maintain a comprehensive audit trail for compliance standards such as NIST, PCI DSS, or SOC2. Additionally, private CAs don’t support external trust, limiting Vault’s usefulness in hybrid or multi-cloud scenarios where customer-facing services demand publicly trusted certificates.
How does IBM Vault orchestrate public certificate authorities?
The new integration positions Vault as a central proxy that securely manages upstream CA credentials and handles complex validation challenges needed for public issuance. By leveraging the ACME (Automated Certificate Management Environment) protocol, Vault automates the entire lifecycle of publicly trusted certificates. Development teams can request these certificates using the same Vault APIs and workflows they already use for private certificates. This unified approach eliminates manual silos and provides a single pane of glass to view every certificate across the organization. The orchestration ensures that validation steps—like domain ownership verification—are handled automatically, reducing human intervention and the risk of errors.
What benefits does centralized certificate lifecycle management provide?
Centralizing certificate management within IBM Vault delivers several key benefits. First, it eliminates the operational overhead of juggling multiple CA portals and manual tasks, drastically reducing the chance of missed renewals and unexpected downtime. Second, it provides a unified governance model: the same security policies, role-based access controls, and audit trails apply to both private and public certificates, making compliance reporting straightforward. Third, it enhances visibility—teams can see expiration dates and certificate status across the entire estate from a single dashboard, preventing the "outage clock" scenario. Finally, it extends Vault’s utility to hybrid and multi-cloud environments, enabling automated public trust for APIs, websites, and external services without leaving the Vault ecosystem. This unified approach simplifies operations and strengthens security postures.
How does this integration improve compliance and audit readiness?
With fragmented certificate management, maintaining a consistent audit trail for standards like PCI DSS, NIST, or SOC2 is challenging because private and public certificates are governed by different tools with different logs. IBM Vault’s public CA orchestration brings everything under one governance model. Every certificate—whether internal or external—follows the same policy templates, and all lifecycle events (issuance, renewal, revocation) are logged centrally. This creates a complete, immutable audit trail that auditors can trust. Vault’s existing features, such as role-based access control and dynamic secrets, extend to public certificates, ensuring that only authorized roles can request or revoke them. Compliance teams can now generate unified reports covering the entire certificate inventory, making it easier to demonstrate adherence to regulatory requirements.
Can teams use existing Vault workflows for public certificates?
Yes, that is a core design goal. IBM Vault’s public CA integration lets developers request publicly trusted certificates using the same APIs, CLI commands, and secret engines they already rely on for private PKI. There is no need to learn new tools or switch contexts. For example, a team that already uses Vault’s PKI secrets engine to issue internal certificates can now add a public CA role and begin requesting certificates for customer-facing services with minimal configuration changes. This consistency reduces training overhead and accelerates adoption. The integration also supports automation via existing CI/CD pipelines—developers can embed certificate requests into their deployment scripts, ensuring that public certs are automatically renewed before expiration just like private ones.
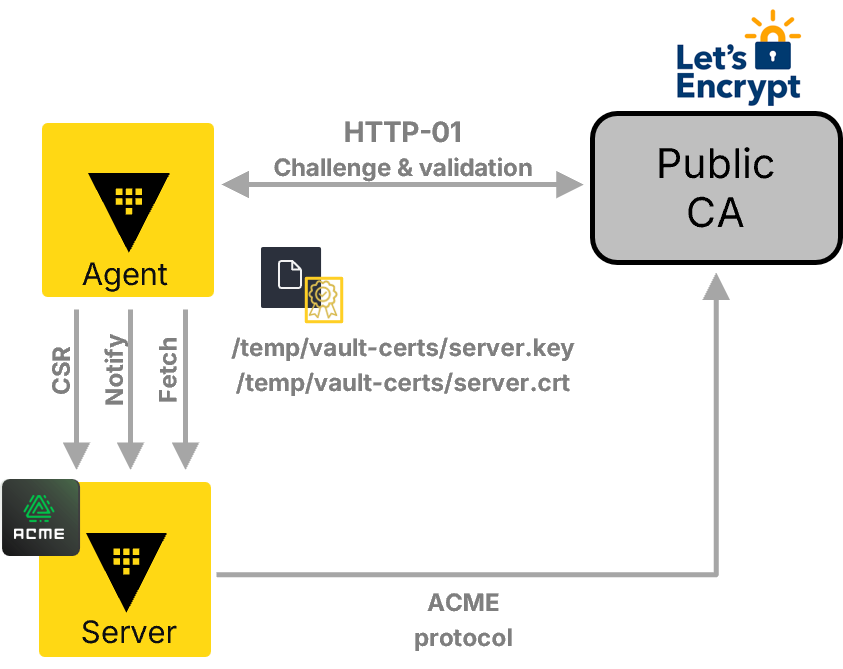
What are the key technical components behind the orchestration?
The orchestration relies on two primary components: the ACME protocol and Vault’s secure credential management. ACME automates domain validation and certificate issuance, allowing Vault to interact with public CAs (such as Let’s Encrypt or commercial providers) without manual steps. Vault acts as a proxy agent that stores the CA’s API credentials (e.g., account keys) in its encrypted backend and handles the challenge-response process (like HTTP-01 or DNS-01) to prove domain ownership. Additionally, Vault leverages its dynamic secret engine philosophy to generate short-lived public certificates where appropriate, reducing the blast radius of any potential compromise. The entire flow is logged and auditable, with granular policies governing who can initiate requests, which domains are allowed, and how often certificates can be issued. This architecture ensures robust security while enabling full automation.
How does this feature address the "outage clock" problem?
The "outage clock" refers to the risk of unexpected downtime when a public-facing certificate expires because teams lacked a central view of expiration dates across different providers. By consolidating all certificates—private and public—into Vault’s single pane of glass, administrators can see every certificate’s expiry status in one dashboard. Vault can be configured to send automatic alerts before a certificate expires or even trigger automated renewal workflows using ACME. This proactive approach eliminates the need to manually track expiry dates across multiple portals. For certificates with short lifetimes, Vault can request new ones daily or weekly, effectively removing the "clock" entirely. The result is zero unplanned outages due to expired certificates, dramatically improving service reliability for both internal and external applications.
What use cases benefit most from unified CA orchestration?
Several use cases stand to gain significantly. E-commerce platforms that manage hundreds of customer-facing websites can automate SSL/TLS certificate issuance and renewal across all domains, ensuring seamless secure connections without manual intervention. Hybrid cloud environments that span on-premises data centers and multiple public clouds can use Vault as a central PKI manager for both internal service‑mesh certificates and external API gateways. DevOps teams practicing continuous deployment can integrate public certificate requests directly into their CI/CD pipelines, automatically provisioning trusted certificates for new microservices or endpoints. Financial institutions and healthcare providers subject to strict compliance regulations can maintain auditable, consistent policies across all certificates. Finally, large enterprises undergoing digital transformation can reduce operational costs by eliminating the need for separate CA management tools and manual renewal processes.